
Keep Email Private: Encrypt Email & Voice Transmission
Protect your business communications with email and voice encryption. Learn tools, best practices, and secure workflows to maintain privacy and compliance.

How to Send PHI Securely by Email: HIPAA Checklist & ePHI Solutions
Secure PHI email guide: HIPAA-compliant workflows, encryption checklist, and tools like Safe Mailer to protect patient data and reduce compliance risk.
Best Encryption Software for Healthcare ePHI
Discover how SafeMailer.io protects ePHI with HIPAA-compliant email encryption. Secure healthcare communications, reduce breach risk, and maintain compliance effortlessly.

Send Sensitive Files Securely: DLP, Watermark, and Encryption
Learn how SafeMailer.io enables secure file transfer with DLP, encryption, and document watermarking. Protect sensitive files, maintain compliance, and streamline secure document sharing.
HIPAA vs PII: Compliance Guide for HR & IT
Understand the difference between HIPAA compliance and PII protection for HR and IT teams. Learn how Safe Mailer helps you secure sensitive email communication and stay compliant with data privacy laws.

Government-Compliant Email Encryption for Public Admin | Secure Communication Solutions
Learn how government-compliant email encryption protects sensitive data in public administration. Discover the steps to ensure secure, compliant, and efficient email communication across agencies.

Zero Trust Email Security: The Future of Protecting Business Communication
Zero trust email security is a modern cybersecurity approach where no user device or system is automatically trusted. Learn how identity authentication, encryption, and access control protect business communication in 2026.
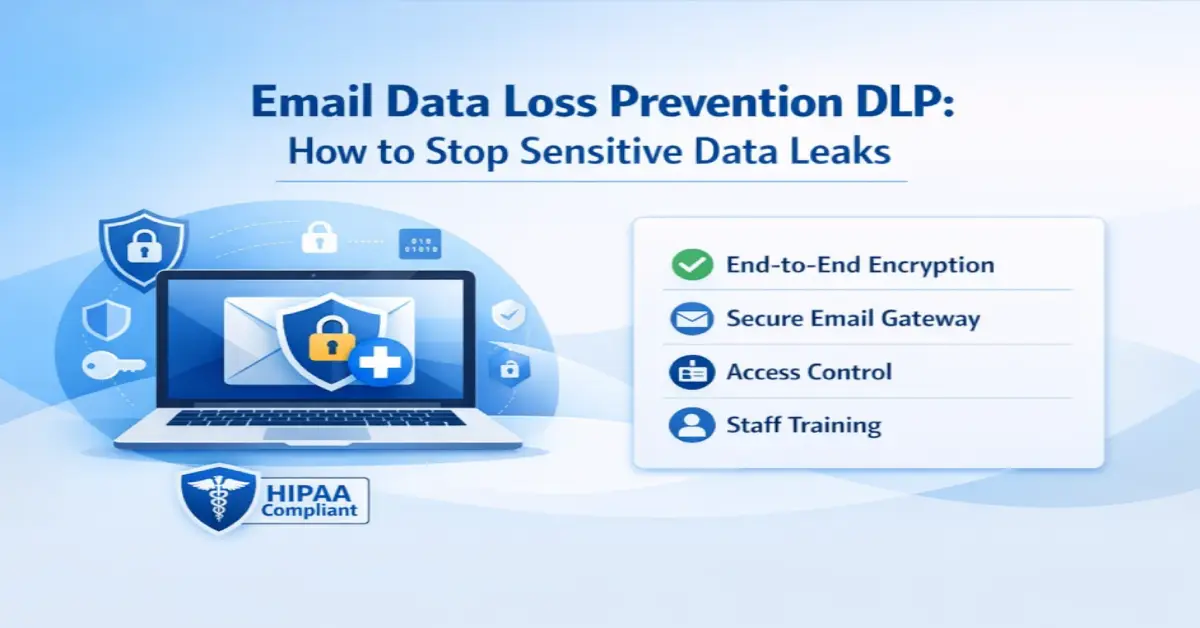
Email Data Loss Prevention DLP: How to Stop Sensitive Data Leaks
Email data loss prevention helps organisations safeguard sensitive information from accidental or deliberate sharing. Discover how DLP solutions use encryption, access controls, and monitoring to prevent data breaches.

Phishing Protection for Email: Protect Your Organization from Advanced Attacks
Phishing protection for email helps organizations identify and avoid fraudulent messages that seek to steal credentials, sensitive data, or financial information. Learn how to defend against AI-powered phishing threats.

Secure Email Audit Trails: Why Businesses Need Email Activity Tracking
Secure email audit trails enable organizations to monitor email flow, track access, and maintain communication records for security and compliance with HIPAA, CJIS, CMMC, FERPA, and ISO 27001.

Email Retention Compliance: How Businesses Manage Secure Email Records
Email retention compliance helps organisations securely store and maintain business email records to meet regulatory needs including HIPAA, CJIS, CMMC, FERPA, and ISO 27001.
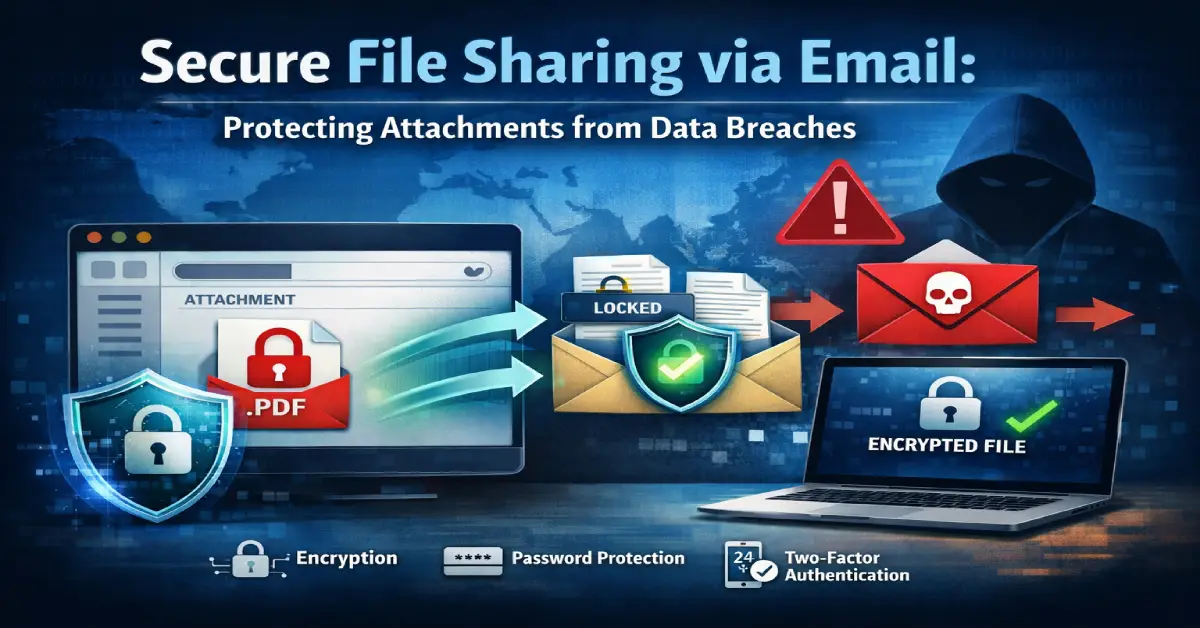
Secure File Sharing via Email: Protecting Attachments from Data Breaches
Secure file sharing via email allows organizations to send sensitive documents safely using encryption, access controls and secure communication platforms to prevent data breaches.

Cloud Email Security Solutions: Protecting Business Communication in the Cloud Era
Cloud email security protects business communication using encryption, identity verification, threat detection, and access control to prevent phishing attacks, data breaches, and unauthorized access.
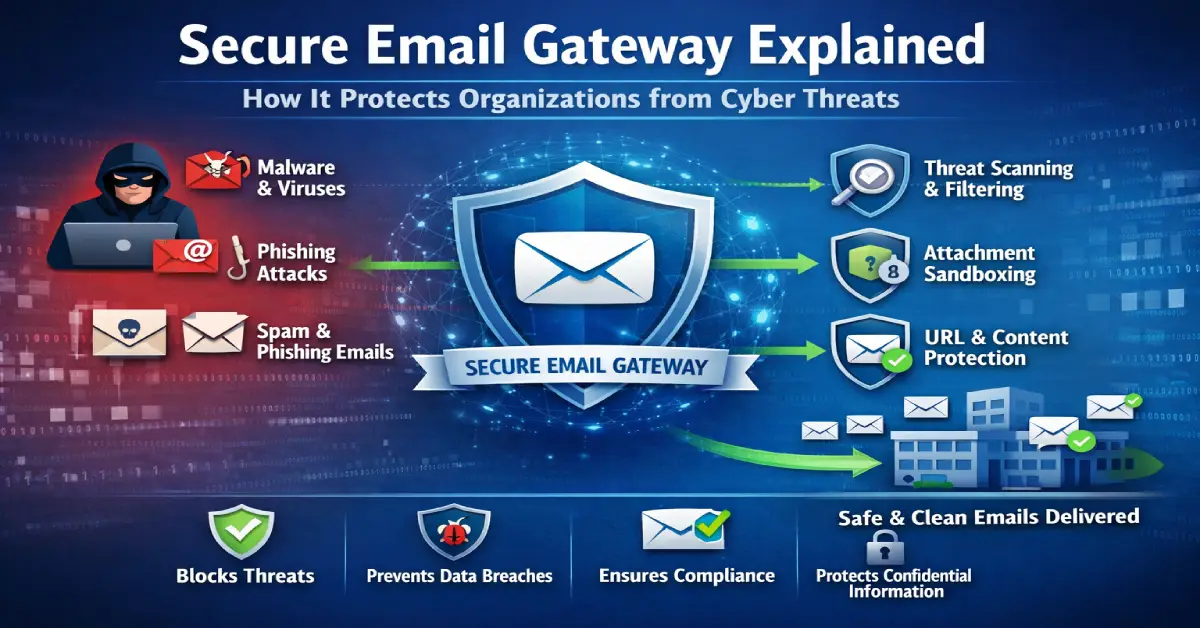
Secure Email Gateway Explained: How It Protects Organizations from Cyber Threats
A secure email gateway filters incoming and outgoing email traffic to detect phishing, malware, spam, and unauthorized data sharing before threats reach users' inboxes.

Insider Threat Prevention: How to Detect and Prevent Insider Threats in Organizations
Insider threat prevention focuses on identifying and stopping security risks from employees, contractors or partners through monitoring tools, secure communication systems, and access controls.

Secure Business Communication During Cyber Incidents: Strategies for Organizations
Secure business communication during a cyberattack is crucial to protect sensitive details and maintain operations. Learn how encrypted email and incident response plans keep organizations safe.

Email Security Awareness Training That Measurably Cuts Risk
Email security awareness training helps organizations reduce human error and phishing risks. Train employees to identify threats and combine training with secure communication platforms like Safemailer.

Supply Chain Attacks: What Every Business Email Security Program Must Know
Supply chain attacks target businesses through trusted vendors using email as the entry point. Learn how to prevent vendor email compromise with encryption, monitoring, and access control.

Data Centric Security: How Zero Trust Strengthens Data Protection Strategy
Data-centric security protects sensitive data at all locations of storage and exchange. Learn how zero trust data protection and information-centric security strategies work with Safemailer.
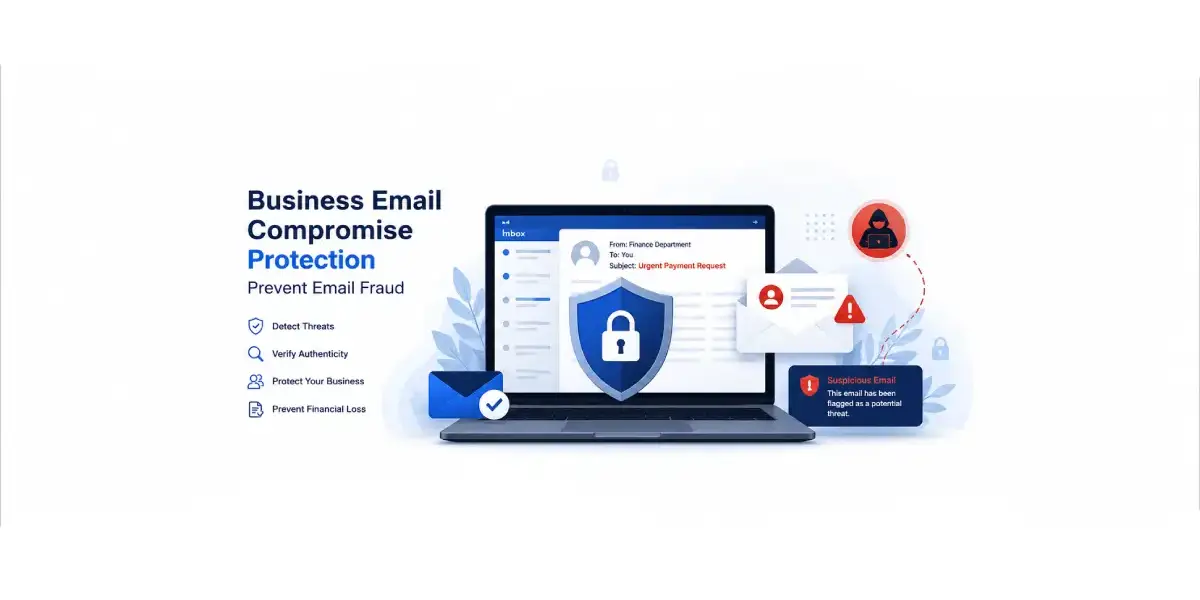
Business Email Compromise Protection: How Organizations Prevent Financial Email Fraud
Business email compromise protection helps prevent financial email fraud. Learn how Safemailer secures communication and stops BEC attacks.

Email Spoofing Attack: How Businesses Detect and Prevent Fake Emails
Email spoofing attacks can be devastating for businesses. Learn how Safemailer secures communication and stops these attacks.

AI Phishing Attacks: How Businesses Can Detect and Prevent AI-Generated Email Threats
AI-powered phishing attacks are becoming more sophisticated. Learn how Safemailer protects against these emerging threats.

TLS Email Security vs End to End Email Encryption: Which One Is More Secure?
TLS email security and end-to-end email encryption each offer unique benefits. Discover which option provides better protection for your organization.

Best Email Security Software for Businesses in 2026: Protect, Encrypt and Defend
Discover the best email security software for businesses in 2026. Protect your organization from phishing, BEC, and data breaches with end-to-end encryption.

Email Encryption Software for Small Business: Stop Breaches Before They Cost You Everything
Protect sensitive emails, stop phishing attacks, and stay compliant with SafeMailer’s email encryption software for small business.

HIPAA-Compliant Email Requirements: A Complete Guide for Healthcare Organizations in 2026
Patient data leaks often start with email. Learn HIPAA email requirements, encryption rules, BAAs, and secure PHI handling for healthcare teams.